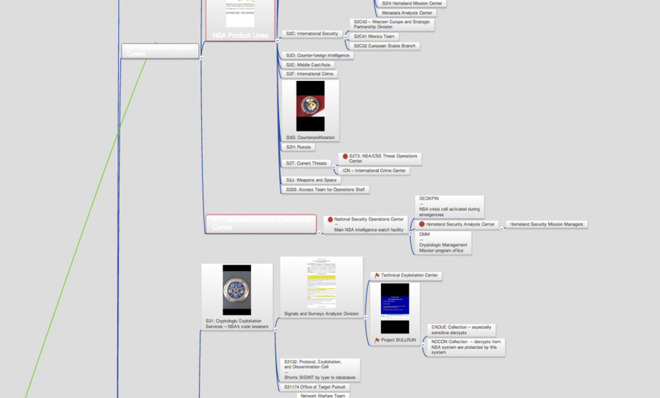
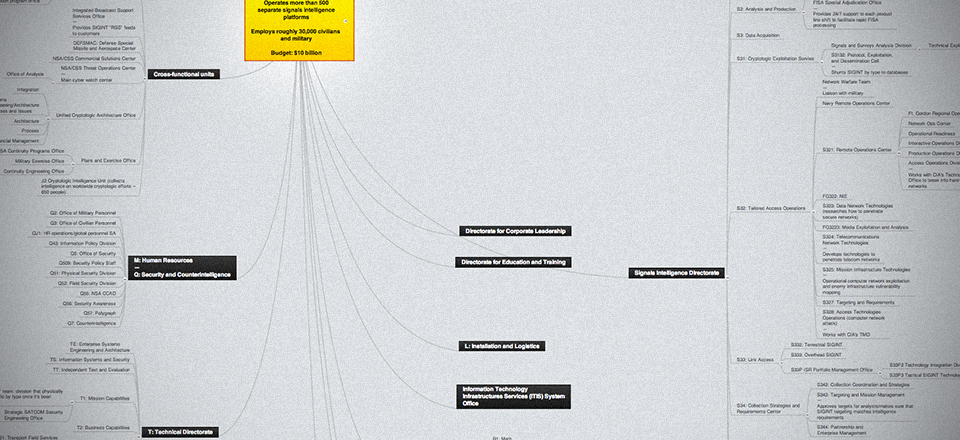
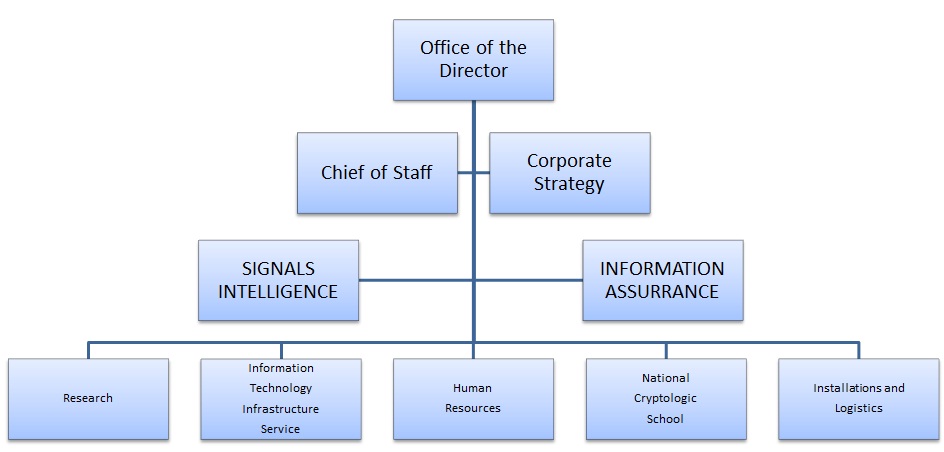
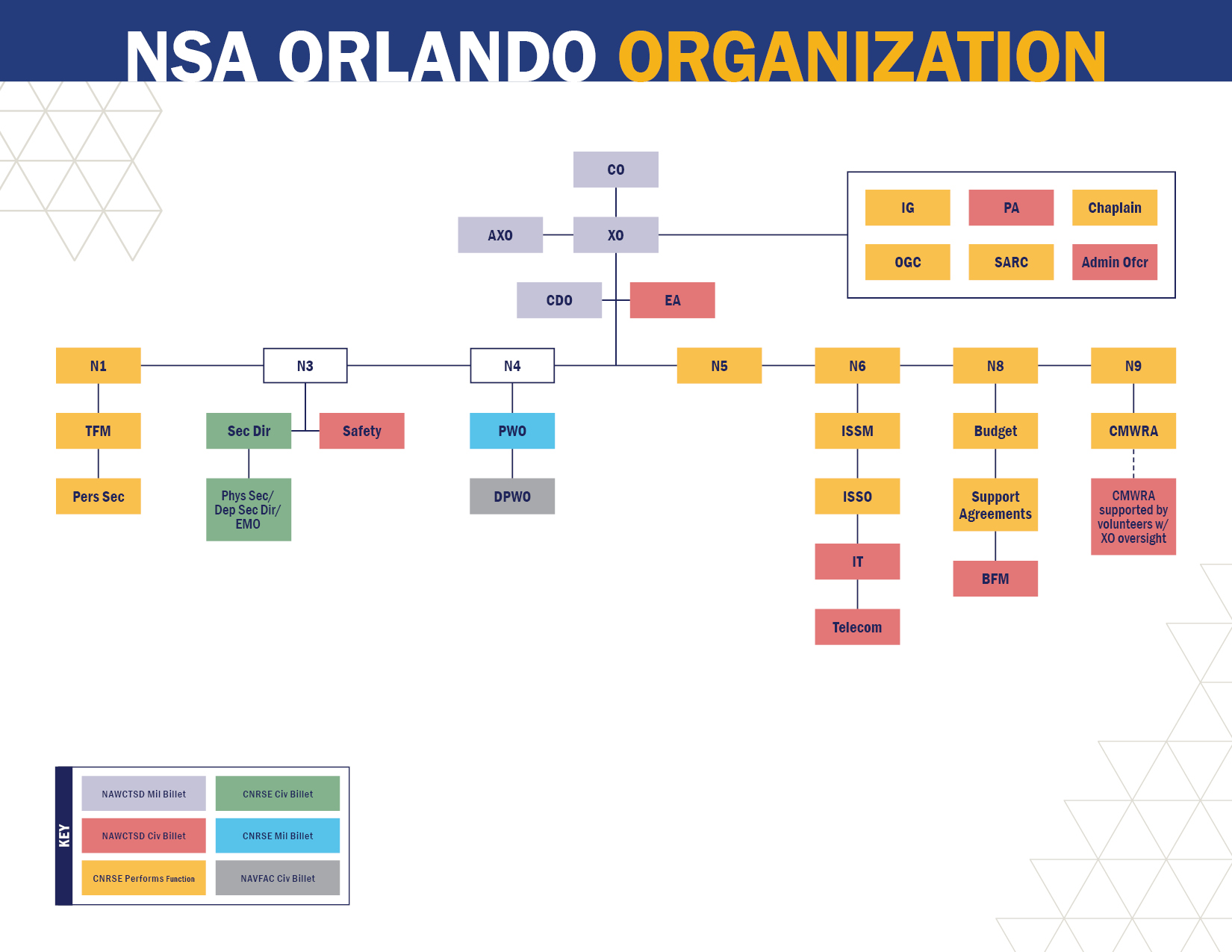
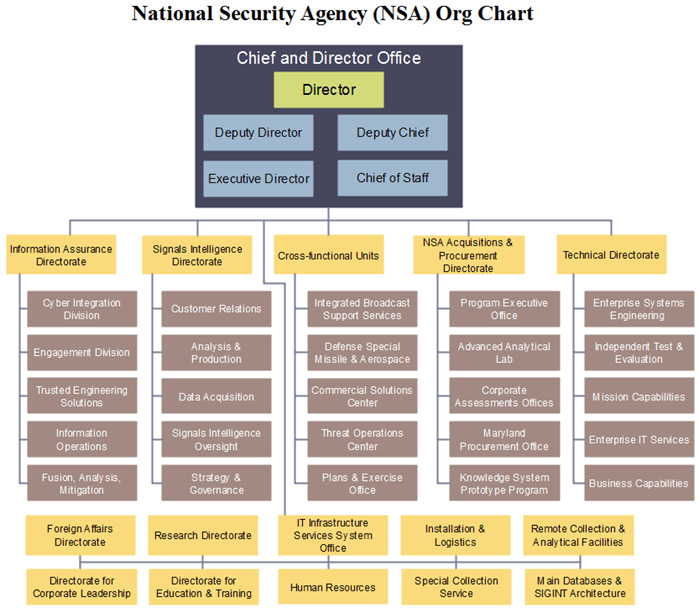
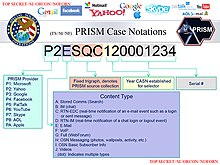
The hierarchical security levels The U.S National Security Agency (NSA)... | Download Scientific Diagram
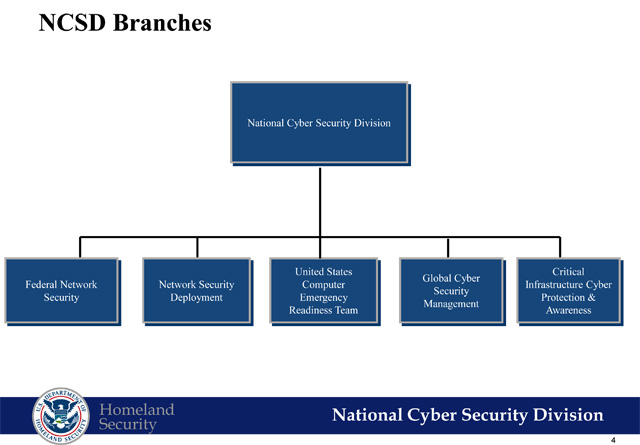
National Security Agency Tasked with Targeting Adversaries' Computers for Attack Since Early 1997, According to Declassified Document
The Puzzle Palace: Inside the National Security Agency, America's Most Secret Intelligence Organization